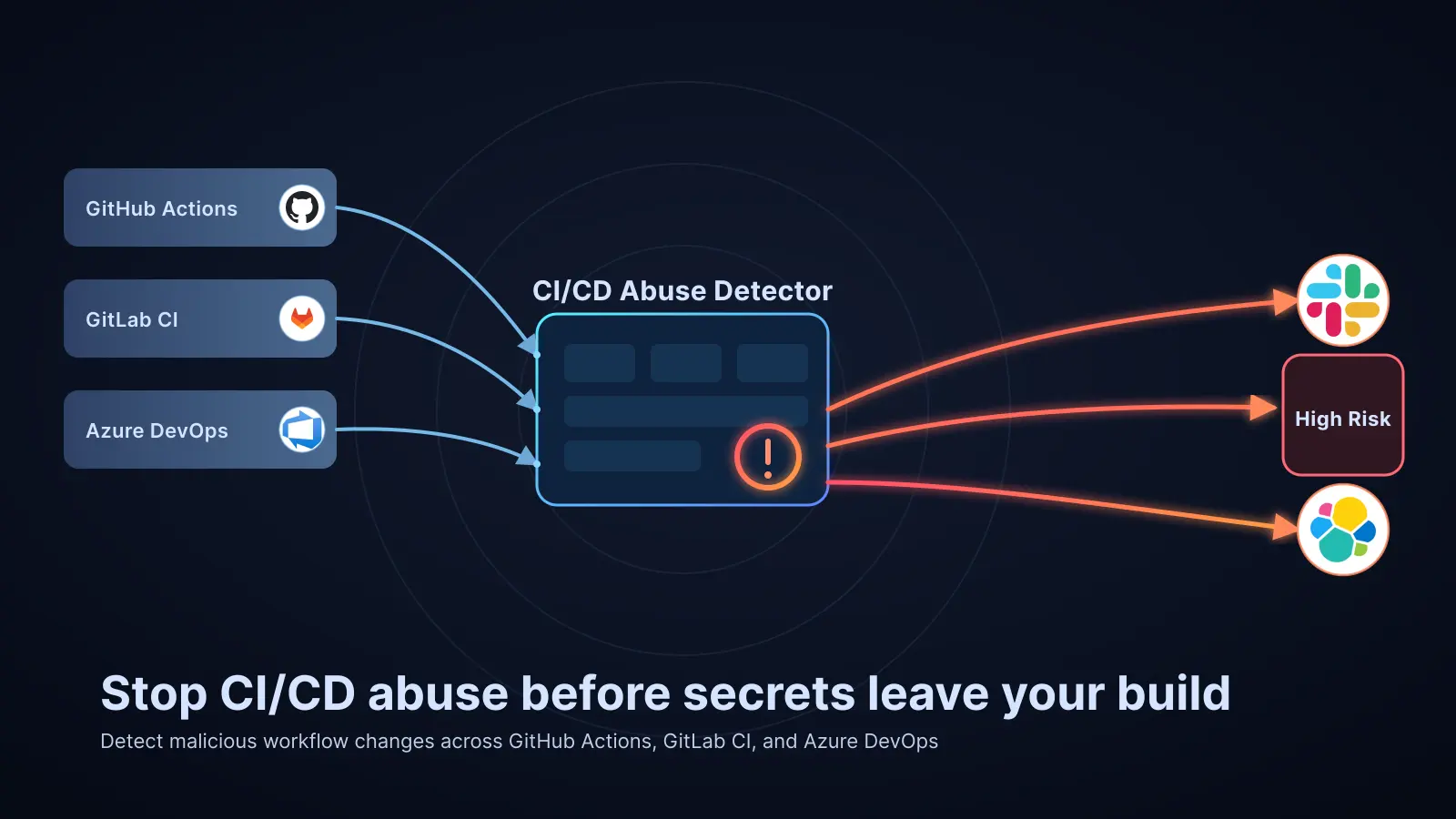
In 2025 and 2026, a quiet but devastating shift reshaped the attacker playbook. Instead of hunting for CVEs on production servers, threat actors began targeting the automation pipelines that build and deploy those servers. A single compromised workflow file can simultaneously expose AWS credentials, npm tokens, Docker Hub passwords, code signing keys, and OIDC tokens — and most organizations have no detection coverage for it whatsoever. Elastic Security Labs is changing that with the open-source cicd-abuse-detector, a drop-in CI template that combines regex-based signal extraction with LLM reasoning to catch CI/CD abuse in real time.
Why CI/CD Pipelines Are the Attacker's New Crown Jewels
Modern deployment pipelines operate with extraordinary levels of trust. A typical GitHub Actions workflow executing a production deploy will hold simultaneous access to cloud provider credentials, package registry publish tokens, container registry passwords, and repository write permissions. The attack surface is not a hardened server — it is a YAML file checked into source control.
The attack chain is deceptively short:
- Stolen developer credentials provide the initial foothold
- A modified workflow file redirects secrets to an attacker-controlled endpoint
- Harvested CI secrets enable lateral movement
- Cloud and production access completes the compromise
Because pipeline files are treated as infrastructure-as-code, security teams rarely apply the same scrutiny to a .github/workflows/deploy.yml change that they would to a firewall rule modification. Attackers have noticed.
Real-World Incidents Driving the Threat Model
The GhostAction Campaign
In September 2025, the GhostAction campaign demonstrated credential harvesting at industrial scale. Attackers compromised 327 GitHub users across 817 repositories, injecting workflow files that silently POSTed secrets to attacker endpoints. The result: 3,325 secrets stolen across a coordinated campaign that went largely undetected until the damage was done.
The Shai-Hulud npm Worm
The Shai-Hulud attack took the threat further by making it self-propagating. The worm harvested GitHub Personal Access Tokens via gh auth token, ran TruffleHog for automated secret reconnaissance, and then used compromised tokens to inject malicious code into other packages owned by the same developer. The first wave alone produced over 46,000 malicious packages across the npm ecosystem.
HackerBot-Claw and the pull_request_target Nightmare
The pull_request_target trigger is among the most dangerous features in GitHub Actions. Unlike a standard pull_request trigger, it executes in the context of the base repository — with full access to secrets — while still capable of running code from an untrusted fork. In February 2026, HackerBot-Claw systematically scanned public repositories for this misconfiguration, deploying five distinct exploitation techniques including poisoned Go init() functions, branch name command injection, filename-based injection, and AI prompt injection targeting Claude-based code reviewers.
In the most severe case, Aqua Security's Trivy repository was fully compromised, triggering a downstream supply chain attack that exposed 33,000 secrets across nearly 7,000 machines. Stolen tokens remained valid for weeks after initial exfiltration — a detail that amplified the blast radius considerably.
The Full Threat Taxonomy
Elastic mapped the CI/CD threat landscape to six distinct attack categories, each with corresponding MITRE ATT&CK mappings:
- Credential harvesting — exfiltrating secrets available in the CI environment (T1552)
- Privileged trigger exploitation — abusing
pull_request_targetand similar misconfigurations (T1059) - Permission escalation — adding
permissions: write-allorid-token: writeto expand blast radius - Runner targeting — redirecting jobs to self-hosted runners with internal network access, or specifying attacker-controlled container images
- Supply chain manipulation — using mutable action references (
@maininstead of SHA-pinned), executing remote scripts viacurl | bash, and poisoning dependency lockfiles (T1195) - Defense evasion via timestomping — backdating commits to make malicious files appear old and trusted, a technique documented in DPRK-linked campaigns (T1070.006)
How cicd-abuse-detector Works
The detector is designed for operational simplicity. It requires no Python, no custom runtimes, and no complex dependencies — everything runs on a standard ubuntu-latest runner using default shell utilities. The only installed tool is the Claude Code CLI via npm, which handles authentication, retries, and model routing.
Stage 1: Filter and Diff
When a pull request opens or a push lands on a protected branch, the workflow identifies changed files across three tiers of CI/CD-relevant paths. The first tier covers core CI files — workflow definitions, pipeline configs, and Makefiles. The second covers build and release artifacts such as Dockerfiles and packaging scripts. The third captures dependency manifests like package-lock.json and go.sum.
Stage 2: Signal Extraction
The tool extracts over 50 regex and metadata signals from the diff before any LLM call is made. These signals cover patterns like:
- Outbound HTTP calls to non-corporate endpoints (
curl,wget,Invoke-WebRequest) - Secret environment variable references piped to network commands
- Use of
pull_request_targetwithout explicit actor validation - Mutable action references using branch names instead of commit SHAs
- Additions of broad permission scopes
- Self-hosted runner or attacker-controlled image references
Stage 3: LLM-Augmented Analysis
Extracted signals and the full diff are passed to Claude for structured threat analysis. The LLM layer handles cases that defeat pure regex: obfuscated base64 payloads, multi-step exfiltration chains, and novel combinations of individually benign signals that collectively indicate malicious intent. The output is a structured JSON report with severity rating, matched signals, attack technique classification, and recommended remediation steps.
Validation Against Real Attacks
Detection patterns were tested against offensive toolkits including Nord Stream and Gato-X, and validated against real incidents including ArtiPACKED and HackerBot-Claw. The project ships with 19 malicious and four benign example diffs modeled after specific documented incidents, alongside an automated test suite that validates every signal against its expected detection outcome.
Deploying the Detector
As a drop-in CI template, integration requires adding the workflow file to your repository's .github/workflows/ directory (or the GitLab/Azure DevOps equivalent) and providing a Claude API key as a repository secret. The template is designed to run as a required status check, blocking merges when high-severity findings are detected and surfacing structured reports as pull request comments for lower-severity signals.
The attack surface isn't a server with a CVE — it's a YAML file. And most organizations have no detection coverage for changes to that file whatsoever.
For teams already using GitHub Advanced Security or similar SAST tooling, the detector complements rather than replaces existing controls. Where SAST focuses on code vulnerabilities, cicd-abuse-detector focuses on the pipeline itself as an attack surface — a gap that remains largely unaddressed by commercial tooling.
Conclusion
The shift toward CI/CD pipeline targeting represents one of the most consequential changes in the attacker playbook in recent years. Incidents like GhostAction, Shai-Hulud, and HackerBot-Claw demonstrate that compromising the build pipeline is often faster, higher-yield, and harder to detect than traditional application exploitation. Elastic's cicd-abuse-detector provides a practical, dependency-light starting point for teams looking to close this detection gap — combining the precision of curated regex signals with the reasoning capability of LLM analysis to catch attacks that neither approach could reliably detect alone. As pipeline-targeting attacks continue to mature, treating CI/CD configuration changes with the same security scrutiny as production code changes is no longer optional.