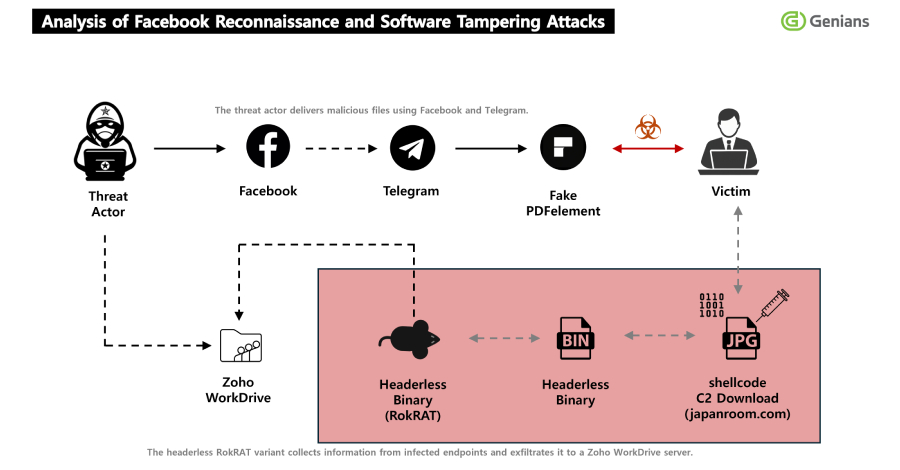
North Korea's state-sponsored threat actor APT37 has adopted a new social engineering tactic, using Facebook accounts to distribute the RokRAT remote access trojan. The campaign, which leverages trojanized versions of the legitimate PDF editing software PDFelement, represents a notable evolution in the group's delivery mechanisms — moving from traditional email-based spear-phishing toward social media platforms to evade detection and build victim trust.
Who Is APT37?
APT37, also tracked as ScarCruft, Reaper, and Group123, is a North Korean advanced persistent threat group believed to operate under the direction of the Reconnaissance General Bureau (RGB). Active since at least 2012, the group primarily targets South Korean government entities, journalists, defectors, human rights organizations, and individuals with ties to North Korean policy.
Unlike Lazarus Group, which focuses heavily on financial theft and cryptocurrency heists, APT37's mandate is primarily intelligence collection. The group is well-resourced, maintains a broad malware toolkit, and continuously updates its techniques to avoid detection by security vendors.
The Facebook Social Engineering Lure
In this campaign, APT37 operators created Facebook accounts on or around November 10, 2025, using them as the initial vector for victim contact. The use of social media is a deliberate tactical choice: Facebook profiles can be made to appear credible through manufactured history, mutual connections, and consistent posting activity, making them far more convincing than unsolicited emails from unknown senders.
Victims were approached through direct messages or posts and directed toward malicious download links under the guise of legitimate software distribution. The attackers impersonated trusted personas — likely researchers, journalists, or professional contacts relevant to the target's field — to increase the likelihood of engagement.
Trojanized PDFelement as the Delivery Vehicle
The payload was bundled inside a weaponized installer for PDFelement, a popular commercial PDF editor developed by Wondershare. Trojanizing legitimate software is a well-established technique because it gives victims a functional application while silently executing malware in the background, reducing suspicion and delaying detection.
When the victim runs the installer, it performs two actions simultaneously:
- Installs a working copy of PDFelement, maintaining the illusion of legitimacy
- Silently drops and executes the RokRAT payload on the victim's system
This technique is particularly effective against non-technical targets who may not monitor process execution or network activity during software installation.
RokRAT: Capabilities and Espionage Functions
RokRAT is a cloud-based remote access trojan that has been part of APT37's arsenal since at least 2017. What distinguishes it from commodity RATs is its use of legitimate cloud services — including Dropbox, Google Drive, OneDrive, and Yandex — as command-and-control (C2) infrastructure. This makes it substantially harder to detect and block using traditional network-based controls, since traffic to these platforms blends in with normal enterprise activity.
Once installed, RokRAT is capable of:
- Keylogging — capturing all keystrokes to harvest credentials and sensitive communications
- Screenshot capture — periodic or triggered screenshots of the victim's desktop
- File exfiltration — searching for and uploading documents, images, and archives matching predefined extensions
- Clipboard monitoring — stealing copied content including passwords and crypto wallet addresses
- Process enumeration — identifying running security tools and adjusting behavior accordingly
- Shell command execution — enabling operators to run arbitrary commands on the compromised host
The combination of these capabilities makes RokRAT a highly effective tool for long-term, stealthy intelligence gathering — consistent with APT37's espionage mandate.
Why Social Media Matters in Modern APT Campaigns
The shift toward Facebook as an initial access vector reflects a broader trend among nation-state actors. Email security gateways, sandboxing technologies, and employee security awareness training have collectively raised the bar for traditional phishing campaigns. Social media platforms, by contrast, are often excluded from enterprise security monitoring, and users frequently operate with a lower threat awareness posture when using them.
APT groups including Charming Kitten (Iran), Fancy Bear (Russia), and now APT37 have all demonstrated willingness to invest the time needed to build convincing social media personas. The low cost of creating accounts combined with the high credibility they can manufacture makes this an increasingly attractive initial access strategy.
Social engineering via social media is not a new concept, but its adoption by sophisticated nation-state actors signals that organizations need to extend their security awareness programs beyond corporate email to include LinkedIn, Facebook, and messaging platforms.
Indicators and Detection Guidance
Organizations and individuals at risk from APT37 — particularly those working in South Korean policy, North Korean human rights, or regional journalism — should take the following precautions:
- Treat software download links received via social media as high-risk regardless of the sender's apparent legitimacy
- Verify software downloads against official vendor websites and check installer hashes before execution
- Monitor outbound traffic to cloud storage services (Dropbox, Google Drive, OneDrive) for anomalous upload patterns
- Deploy endpoint detection and response (EDR) solutions capable of detecting RokRAT's known behavioral patterns, including its cloud-based C2 communications
- Review and restrict personal use of social media on corporate devices, particularly for high-risk personnel
Security teams should also hunt for processes spawned from installer executables that subsequently establish persistent connections to cloud storage APIs — a hallmark indicator of RokRAT infections.
Conclusion
APT37's use of Facebook social engineering to deliver RokRAT through trojanized PDFelement installers underscores the group's operational sophistication and willingness to adapt. By moving initial contact to social media and hiding malicious activity inside legitimate software, the group bypasses many conventional defensive controls. For individuals and organizations operating in APT37's target sectors, this campaign is a reminder that the attack surface extends far beyond the corporate inbox — and that software provenance verification and cross-platform security awareness are essential components of a modern defense posture.